Blog
A Hypothetical Case of a Phishing Attack
November 23, 2018
Let’s say hypothetically that we receive an email from an old university email that looks like this:
How would an average student view this?
Looks 👌legit.👌
Now what though? Maybe this email just came from someone who graduated 5 years ago and really likes to use their birthday as their password. Or, the email could have been spoofed?
Something has to be done about this hacker... How about we invite Evan Conrad of Segment to join in on the fun?
Let’s say, purely for story-purposes, that we clicked on this “verify now” business to see what all the fuss was about.
Continue Reading →
Digital Signatures, HMACs and Hashing
November 8, 2018
Background
There are a few key terms that should be known before reading this article. I will briefly explain these.Symmetric vs Asymmetric Encryption


Symmetric encryption takes a value, known as m and encrypts it with the key, K . To decrypt it, use K to go back to the original value. A basic example of a symmetric encryption cipher would be the Cesar Cipher.
Asymmetric encryption (otherwise known as Public Key Cryptography) has two different keys: a public key and private key. In order to encrypt the data, use the public key. To decrypt it, use the private key. An example of this is the RSA algorithm.
Both symmetric and asymmetric serve their role and have their issues. In the early days of cryptography, their common problem: how to share the key? This plagued people for generations! The key cannot go alongside the message...The key also cannot be sent in a different letter, as it can still be intercepted and read...This is where public key cryptography comes into play. Because the public key is known and available, then encrypt the data with the public (known) key. If the a malicious adversary tries to intercept the message it will not matter, as only the receiver will have the private key to decrypt the message. The key exchange issue was solved with the creation of public key cryptography.
Even though public key cryptography solved the key exchange problem, symmetric ciphers are still used today. Most asymmetric encryption algorithms are extremely expensive to compute. In the example of RSA, the encryption scheme looks like messagee (mod n). The issue comes with the messagee, where e is an extremely large value. So, encrypting all data using Public Key Cryptography is not a viable option. Because of this, symmetric key ciphers are still used to encrypt message information. Practically speaking, asymmetric encryption is used in order to exchange keys, while symmetric algorithms use the transferred key in order to encrypt the data. Now, that receiver knows the key, there is a very small chance for an adversary to be able to read the message.
Public Key Infrastructure (PKI)
The system that provides the Public Key Encryption keys and digital signatures for an entity is the PKI. The purpose of the PKI is to maintain and manage the keys/certificates that are in the system. By doing this, a trustworthy networking environment is created for using the cryptographic systems. To sum it up, the PKI ensures that the entity saying they own the public key, to encrypt the data to send to the other party, is actually the entity they claim they are. The most well known of this is implemented within the browser ecosystem, known as TLS (Transport Layer Security).
Hashing, HMAC and Digital Signatures
In order to have a consistent way to discuss the differences between the three methods, I will use the example of transferring a file throughout the post.
Hashing
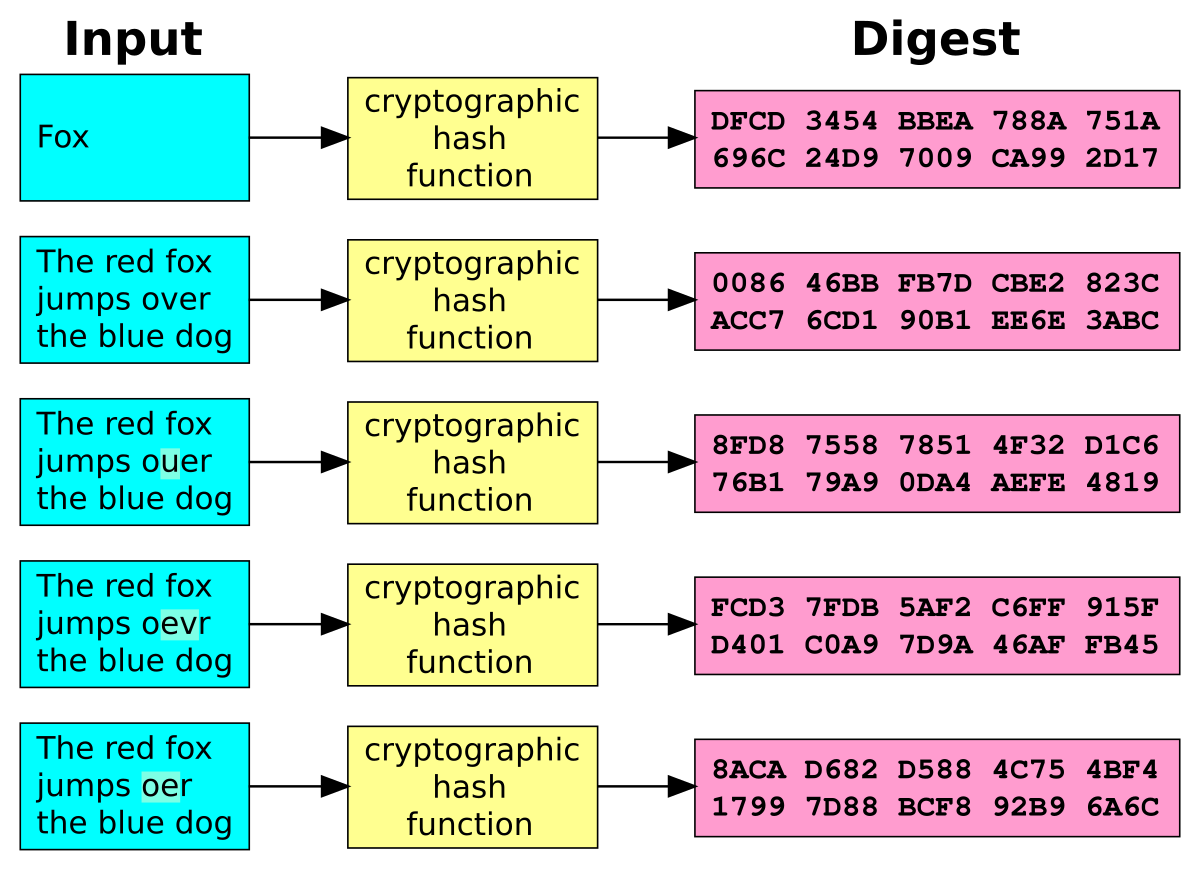
In general, hashing is a way to map an arbitrary sized data value to a fixed size (as shown in the image). In terms of security, a hash function allows someone to easily verify that two values are the same, without actually knowing the value itself. Typically, cryptographic hash functions are known as 'one-way' functions. This means that a value is easy to hash, but near impossible to go from the hash to the original value. Another interesting property of hash functions can be seen in the picture. If a single bit is changed, then it dramatically changes the result of the hash function. A few examples of cryptographic hashing functions are SHA2, MD5 and SWIFFT.
Hashing is used for ensuring the integrity of the data. Or, they can be used to store passwords securely with a few other modifications (salts). As this allows for the password to easily be verified against yet near impossible to get the original password back(assuming a strong password).
In the example stated above, the sender would send the file, alongside the hash of the file. The receiver would then use the same hashing function (as the sender) on the file. If these two hashes are the same, then the file has not been tampered with.HMAC
A message authentication code (MAC), is a small value used to authenticate a message, meaning to confirm that the message came from the actual sender. Now, an HMAC (Hashed Authentication Message Code) is a message authentication code that uses a cryptographic key alongside a hash function to determine the integrity and authenticity of the message.
In the example, the sender and the receiver would both share a private key for a symmetric encryption algorithm. Then, the sender would hash the file with a strong cryptographic hash function. From there, the hash of the file is encrypted with the private key. The receiver can then decrypt the hashed value with the shared key to have V1. The receiver then will use the same hashing function (as the sender) on the file to get V2. If V1 and V2 are the same, then we know that the file came from the correct entity and that the file has not been tampered with because of the usage of a secret key. HMAC's are used to determine both the integrity and authenticity of the file.
Digital Signatures

A digital signature is a scheme for presenting the authenticity of a digital message or document. Digital signatures use asymmetric cryptographic schemes.
Within the realm of digital signatures, a PKI (Public Key Infrastructure) is needed in order to ensure that the public key belongs to the correct entity. For example, Amazon has a public key that is used to encrypt data being sent to them. However, what stops a malicious actor from giving a victim user a public key, claiming that it is Amazons? If this happened, then the malicious actor can read the message sent to Amazon. This is the reason for the PKI system.
In terms of the example, the sender needs to have a asymmetric encryption scheme that allows for digital signatures, such as RSA. Once the keys are created, then the fun begins! To start with, the sender hashes the file. This is where the HMAC and digital signatures differ: the sender uses their private key (that only they know) to sign the message, instead of a symmetric key. Now, the receiver of the message will use the public key to decrypt the hash, V1. The receiver then hashes the file themselves, to get V2. If V1 and V2 are the same, then we know a couple of things: the file has not been tampered with and the sender is truthful.This demonstrates integrity, authenticity and non-repudiation for the file. More on these three terms below...
Differences
Even though the differences may seem very subtle, they are quite substantial. There are three main parts to this: integrity, authenticity and non-repudiation. The definitions about these three concepts came from here.
| Security Goal | Hash | HMAC | Digital Signature |
|---|---|---|---|
| Integrity | ✓ | ✓ | ✓ |
| Authenticity | ✓ | ✓ | |
| Non-repudiation | ✓ |
Integrity
Integrity is defined as "Can the recipient be confident that the message has not been modified?" All three of the methods described above ensure the integrity of the file because if the file is altered, then the hash function will give a different value in return. The integrity problem is the easiest part to solve.
Authenticity
Authenticity is defined as "Can the recipient be confident that the message originates from the sender?" A hash function can show that the file has not been tampered with. However, nothing prevents a malicious middle man from intercepting the message and hash to replace both the message and hash in the original message with their own. Because of this, just using a hash function lacks authenticity. Both the HMAC and digital signature provide this protection because of the keys used to encrypt the hash are unknown to the malicious adversary. Both the HMAC and digital signature prove that the message came from the expected sender.
Non-Repudiation
We define non-repudiation as "If the recipient passes the message and the proof to a third party, can the third party be confident that the message originates from the sender?" The only one of the three that can actually prove this is the digital signature. The reason for this is because an HMAC function uses a symmetric key, while a digital signature has an asymmetric key. With an HMAC function, the recipient of the message could alter the message however they please, because they have the key to do so. The recipient could then write whatever they want as the sender. However, with a Public Key Cryptography system, only the sender has the private key. In practice, this means that only the sender can encrypt the message! So, because the recipient cannot encrypt the message, allowing for the non-repudiation factor of this system. Wow, public key cryptography is amazing!
Issues
Digital Signature Size
One known issue with public key cryptography is how large the keys tend to be. Unlike MAC's and Hash functions (which provide a fixed length value) a digital signature is quite large and has a variant in size. Further, because of the major size, calculating a digital signature is incredibly slow.
Scaling
In order to be a viable option algorithms must scale for a wide adoption. In the case of Public Key Cryptography, it works quite well. Only a single public and private key are needed for the task, then any sender can use the public key to encrypt the hash. A PKI system takes care of exchanging public keys for the data to be encrypted. However, HMAC functions do not scale well in the PKI example because symmetric keys must be known by both parties. This means that every sender/receiver pair must have their own private key. The difference is that Public Key Cryptography has two keys (public and private) while HMAC must use n number of keys, where n is the number of receipts.
Replay
This data protection algorithms work extremely well. However, they all fail on one problem: replay. The replay attack is defined as "a malicious adversary sending the same message, found by passive listening on original messages." However, the fix for this uses timestamps and nonces (number used once) to ensure the message is the request that the user intended to sent. So, if the message is attempted to be sent again, the receiver will reject the message for being used previously.
Conclusion
I would like to give a major S/O to my amazing cryptography Professor Paul De Palma (Gonzaga U) for his incredible job at teaching me the basics of cryptography! With the knowledge simply learned from his class, I was able to do extremely well on a set of cryptography based interview problems.
Digital signatures, hashes and HMACs all have great use cases, if used in the proper setting. A practical example is within TLS (Transport Layer Security in the browser). Entity (such as a company) authentication is performed using a digital signature. However, the messages themselves are protected by using a fast MAC function. Hope you enjoyed! Cheers from Maxwell Dulin (ꓘ).
Analysis of Livestream Exploit of Drobo5N2 by ISE
September 28, 2018
This is going to be another analysis over the livestream event done by the
Rick Ramgattie is a security analysis at ISE, where he does security consulting and research within the cyber security space, including publications in CSRF by deciphering Java RNG, routers and embedded devices. Throughout the livestream I was really amazed at the amount of awareness over explaining each and every step to the audience in such a simple and elegant way. I would highly recommend watching the video on the livestream; this is only meant to make it easier for someone to follow. So, thanks so much for this fantastic exploit and explanation Rick! Also, thanks to Ian for helping creating the exploit!
My Thoughts
This video was quite amazing at demonstrating the vulnerability. However, I'd like to set the bar even lower for people/ take notes for myself to use in the future. Below are my takeaways from the penetration test. To start with, I will talk about basic terms and technologies used to have a better understanding of the situation and tools used to exploit the device.
Terminology/Technology
NAS (Network Attached Storage)
A good link for describing a NAS can be found here. Essentially, a NAS is a computer level, file storage system that can be viewed remotely.
Basic Networking
In order to connect to an application or service, we define these areas as IP addresses, which can correspond to domain names. A port is a particular socket on the IP being connected to. An example of a common port is http, which by convention, used on port 80. The Nmap tool is used in order to scan for the open ports and what services they are each running. A tutorial can be found at https://github.com/mdulin2/nmap_writeup.Attacking Methodologies
There are three types of attacking: white, grey and black box. With a black box attack, an attacker only has the application itself, with no specs, code or anything on how it works. Black box attacks tend to only find the low hanging fruit because it is difficult to have a firm grasp on the system. A white box attack is the opposite; the attacker has the code for the device itself! This gives the attacker the ability to understand the logic and implementation of the system, giving them a much greater ability to exploit something on the system. ISE likes to do a white box analysis on devices because they like to find the issues with the underlying structure of the device, as opposed to easy, low hanging fruit. Often, the most serious attacks take a very deep level of understanding that cannot be obtained with a black box approach. A grey box is simply a mixture of the two above.
XML (eXtensible Markup Language)
A language that is commonly used to transport data in a flexible, agreed upon and organized manner. XML is similar to JSON in the way that it was created to be a unified way to transfer data. XML looks like HTML in that it uses tags such as <Attribute>.
Wireshark
A network protocol analyzer. The tool allows for someone to view, organize and analyze the individual packets that were being sent on the network. These captures can happen in real time or be saved for future analysis.
Vim
Vim is an amazingly simple text editor that runs within the terminal. Although it may not be the easiest tool to use, the usage by Rick shows off the incredibly fast capabilities of Vim within the terminal. Other similar tools include Nano and Emacs.
Netcat (nc)
A common computer network utility for reading and writing connections. Netcat is extremely versatile, making it a useful tool within any hackers toolbox.
Reconnaissance
To start with, the ISE folks wanted to understand how the Drobo device worked. Without understanding what the device is capable of, there is no way to know how to exploit it. Some penetration testers will go as far as to say the reconnaissance step is the most important; it allows an attacker to establish possible weak-points in the service.
Continue Reading →
Coffee With CISO of Starbucks
September 18, 2018
Several weeks ago, I had a fantastic opportunity to chat with the CISO(Chief Information Security Officer) of Starbucks, Dave Estlick. If you do not know who this man is, he has quite the resume! He has worked at Sun Microsystems, Boeing, Amazon...He is on the board of 7 different cyber security groups, including PCI(Payment Card Industry). This guy has been around the block! In terms of security, he has been in the game since the beginning; he started his career in security around the year 2000. If you would like to know about the man, his Linkedin is https://www.linkedin.com/in/destlick/.
Expectations
Honestly, I expected a pretty quick conversation with the guy. I had forced a very strange connection with the man in order to get him to meet with me. So, I figured I would have the pry the answers out of him then he would leave. However, Dave was more than willing to talk about his career and how he got there, which was very much appreciated.
Secondly, I also expected to have more of a technical talk. But, what we talked about was much more valuable; I saw into the world of how to be successful and to be a winner! The advice below is directly from a man who is the CISO of Starbucks; also known as a man at the top of the industry. Most of these concepts and ideas do not just have to do with the world of cyber security, but to life in general.
Initial Words
Before I could even ask Dave a single question he came out and said the three most important things right off the bat.Problem Solver
No matter how experienced someone is in the field, a new and different experience will come up. So, now what? The situation is new and difficult to handle. However, this is where the problem solver comes into play. Someone who is marketable, as any sort of professional, should be able to fix issues that are happening in the company. No matter the problem: a security breach, internal issue with employees or anything else, being able to solve problems is very valuable.
Being a problem solver, though, is not a simple skill to develop; this requires dedication to excellence, creativity and a dedication to the profession. If you are able to call yourself a problem solver, then you are in a good place!
Self-Educator
If you are waiting for your employer/school to teach you something then you have likely gone wrong. The people who are willing to go above and beyond by teaching themselves are extremely valuable. Why so?
Continue Reading →
Caught Dead In The Water
September 13, 2018
The Situation
Even though I love reading every security blog that I can find, I got tired of checking every single blog every day! With blogs like the googleprojectzeroday only posting once every couple of weeks, it made sense. So, I created a piece of software that automates this process of checking the blogs then sends me an email about my updated blogs of the day! I currently have an easy to use CLI to add, remove and format the definition of 'updated'. Anyone who wants to use the script can find it at https://github.com/mdulin2/security-blog-updates. I find it very useful and I hope everyone else does.
Dead In The Water
This morning, I checked my email box to see that my automatic morning email had not been sent for my blogs. So, I checked my server to see what had happened. However, I found something that was terrifying; a file, that I had not created called dead.letter.
Crazy thoughts started running through my mind! Who would want to hack me? How did they get in? Why did I not make this more secure? What a clever name... Dead.letter; probably telling me I am dead in the water, holding my website ransom! So, after a while, I decided it was best to look into what the damage was. But, all the letter said was "UnicodeDecodeError: 'ascii' codec can't decode byte 0xc2 in position 13: ordinal not in range(128)".
At that point, I realized that my code had a mistake in it! Yipeee! My site had not been hijacked; dead.letter was just a log for sending email with SMTP. The error was caused by my script writing to a file with the current unicode encoding, without converting to a ascii character set for the text file. This ending up being a trivial fix.
Conclusion
You are likely not being hacked, most of the time. However, it is good to be cautious! In the era of Ransomware and botnets, every computer has a large price tag on it. I also learned what dead.letter was today; I can guarantee that I will never forget what it is either.




