Blog
A Hypothetical Case of a Phishing Attack
November 23, 2018
Let’s say hypothetically that we receive an email from an old university email that looks like this:
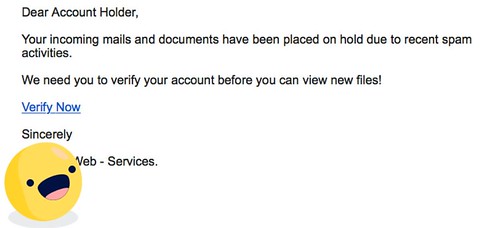
How would an average student view this?
Looks 👌legit.👌
Now what though? Maybe this email just came from someone who graduated 5 years ago and really likes to use their birthday as their password. Or, the email could have been spoofed?
Something has to be done about this hacker... How about we invite Evan Conrad of Segment to join in on the fun?
Let’s say, purely for story-purposes, that we clicked on this “verify now” business to see what all the fuss was about.
Password Please
It may look something like, this:
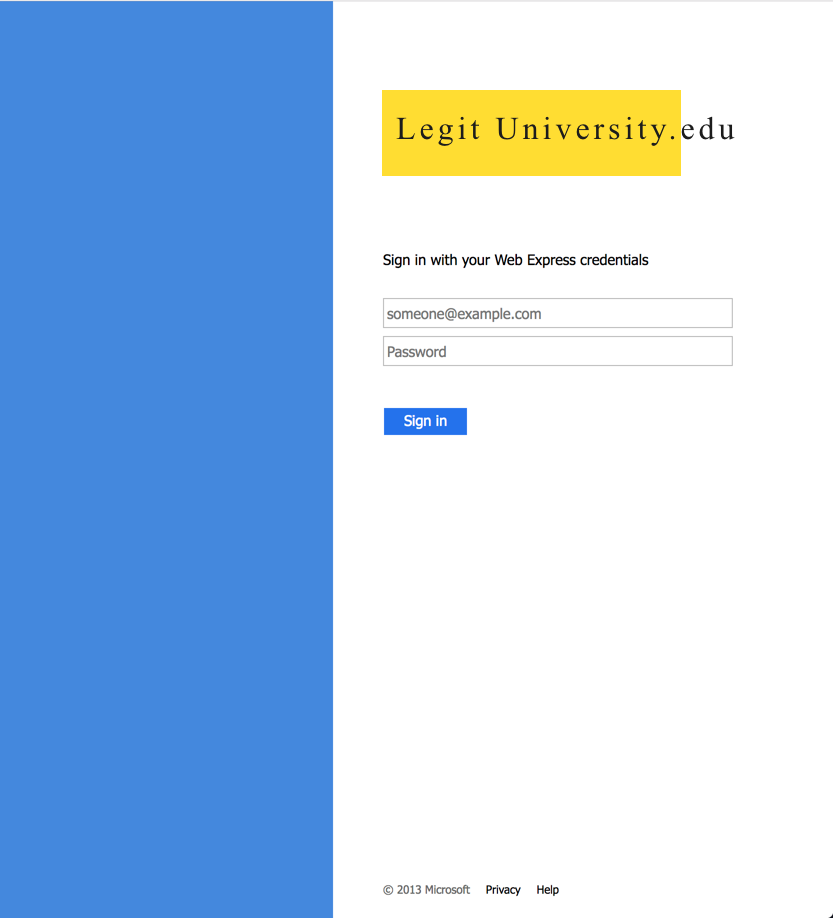
And maybe it's coming from some url like:
https://bougurh.club/%20yaga/legit.edu/index.html
Let's Do Some Peeking
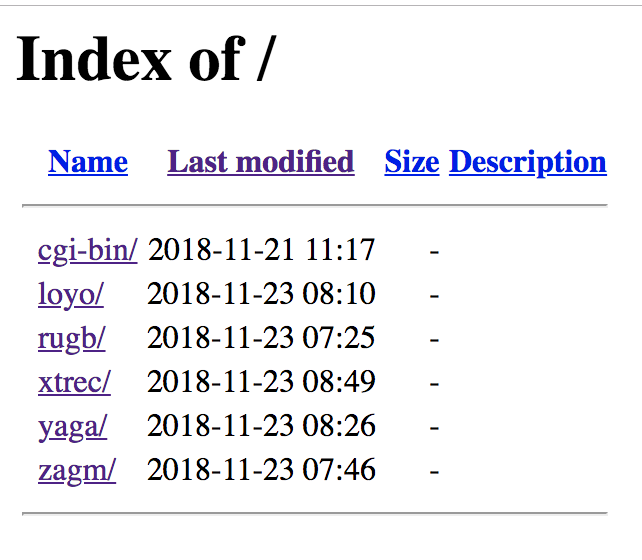
We should checkout who this https://bougurh.club site is at the root.
They just show you their structure. They're even hitting multiple universities at once:
Info On the Hacker
The site uses https? So, where did the certificate come from. Turns out from a quick search on SSLhooper that the domain was generated using AutoSSL. The cert was recently created (three days ago); only lasts 90 days. I wonder if some changes in the PKI will ever be made to help prevent attacks such as these.
What else? He is using Secured Servers LLC to host the website. This hosting company is largely known for the spam that is sent from it. So, this makes sense that the legendary hacker here is using this hosting provider.
What is running on this box? Let's use nmap to find out!
Nmap output: PORT STATE SERVICE 21/tcp open ftp 22/tcp open ssh 53/tcp open domain 80/tcp open http 110/tcp open pop3 111/tcp open rpcbind 143/tcp open imap 443/tcp open https 587/tcp open submission 993/tcp open imaps 995/tcp open pop3s 3306/tcp open mysql
Services are open everywhere! Maybe one of these will allow us to gain more info? The FTP server and IMAP (email) are both accepting connections. MySQL is running but does not accept remote connections. After trying to connect to all of these using netcat, all of the services had up-to-date versions with authentication with non-trivial passwords. So, on to the next idea.
What Happens When We Log In?
If we try to enter our details into this site, they try to send a POST to a /post.php which just logs the email and password in plaintext, then redirects us to Microsoft Outlook.
Since most students are already logged into their emails. So, it will appear as if the login worked. Victims might not even notice!
And that's... probably bad.
What Can We Do?
Well we can reach out to the IT departments of the schools. But it's the holidays and no one's going to get back to us.
We could reach out to their domain name provider. But again... holidays.
Host provider? Let me spell it out for you:
them.stuffFaceWithTurkey()
So What Could We Really Do?
Well, we could send them ascii art pictures of dogs:
_.-.._ _._
_,/^^,y./ ^^^^"""^^\= \
\y###XX;/ / \ ^\^\
'\Y^ / .-==||==-.)^^
,.-=""""=-.__ /^ ( ( -/<0>++<0>(
.^ .: . . :^===(^ \ ( ( /'''^^^^^^^)
/ .: .,GGGGp,_ .( \ / /-(o'~'o))
.^ : . gGG"""YGG}. \ ) / / _/-====-\
/ (. .gGP __ ~~ . .\ \ ( ( _.---._)
/ (. (GGb,,)GGp. . . \_-^-.__(_ /______./
( \ . '"!GGP^ . . . . ^=-._--_--^^^^^~)
( /^^^\_. . . . . . . . . . . . . . . . )
) / /._. . . . . . . . . . . . . ._.=)
\ / | ^"=.. . . . . . . ._++""\"^ \
\ | | )^|^^~'---'~^^ \ )
) / ) / \ \ \
|' | \ /\ \ ( /
| | ( ( \ . .\ | (
) | ) ) ^^^^^^ | |
/. . \ | '| ) (
^^^^^^ ) \ /. . \
/ . . \ ^^^^^^
^^^^^^^
s'ko go dem zig zags
zippity zooms
If I was a l33t hacker, I would defintely love to see my victims best friends sending me ascii art pictures of dogs as the username and randomized compliments and fun facts as the password:
const passwords = [
'hello mr hackerman we love you very much',
'mr hackerman come join our club, we need new members',
'do it dude we wana be your friends',
'did you know bunnies actually die if they eat too many carrots',
'mr hackerman dont feed bunnies too much lettuce; its like candy for them and theyll get fat',
'mr hackerman feed your bunnies a lot of lettuce so theyll get fat its adorable',
'mr hackerman you should rate our bunnies 0-10 how good of a bunny is it (this is a test the answer is 11)',
'if our ascii art doesnt show up correctly blame cpanel not us',
'mr hackerman did you red pandas use their tails as blankets',
'mr hackerman did you know sheep can recognize facial expression and they like smiles',
'mr hackerman did you know polarbears touch noses when they meet each other',
'mr hackerman did you know baby elephants suck on their trunk for comfort',
'mr hackerman did you know that monkeys make snowballs and throw them at each other',
'mr hackerman did you know that a cat has been the mayor of a town in alaska for 17 years',
'mr hackerman did you know that dogs exist',
'mr hackerman did you know that cats exist',
'mr hackerman did you know that you can save 15% or more when you switch to geico'
]
And nothing would make my day more than seeing my logs flooded so that it's hard to read any "legit" requests.
But, the l33t hacker could just filter this out. What else could we do?
Instead, what if we sent them "real" requests? We could craft a little cURL like this:
const curl = (username, password, userAgent) => {
const cmd = `curl '${kiddysite}'
-H 'User-Agent: ${userAgent}'
-H 'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8'
-H 'Accept-Language: en-US,en;q=0.5' --compressed
-H 'Referer: https://bougurh.club/%20yaga/someuni.edu/Sign-In.html'
-H 'Content-Type: application/x-www-form-urlencoded'
-H 'Connection: keep-alive'
-H 'Upgrade-Insecure-Requests: 1'
--data
'UserName=${username}&Password=${password}&AuthMethod=FormsAuthentication'`
exec(cmd, (err, stdout, stderr) => {
console.log(`stdout: ${stdout}`);
console.log(`stderr: ${stderr}`);
if (err !== null) {
console.log(`exec error: ${err}`);
}
})
}
Then, we could use something like faker.js to generate real sounding email addresses like:
jwhite@someUniversity.edu mMcarthy2@otherUniversity.edu
Then we could generate "real sounding" passwords with a little function like this:
function randomFakePassword() {
switch (Math.floor(Math.random() * 10)) {
case 0:
return randomFakeEmail()
case 1:
return faker.date.past() + faker.commerce.color()
case 2:
return faker.hacker.abbreviation + Math.floor(Math.random() * 10)
case 3:
return faker.address.streetAddress()
case 4:
return faker.address.country() + Math.floor(Math.random() * 10) + faker.address.state()
case 5:
return "passw" + Math.floor(Math.random() * 10) + "rd" + faker.commerce.color()
case 6:
return faker.company.companyName()
case 7:
return faker.finance.bitcoinAddress()
case 8:
return faker.address.streetName() + Math.floor(Math.random() * 10) + "pass"
default:
return faker.finance.accountName()
}
}
For extra fun, we can even create different user agents using faker again.
Then, we could create random timeouts and drip requests in as the day goes on. That way our hacker gets "caught" with the ascii art, but also can't easily filter out the "good" data.
Is this actually doing anything?
A lot of l33t hackers are newbs. They're copy/pasting code and setting things up pretty poorly. They're not experts.
That means they're often skittish. In this case, it only took a hundred requests or so before they shut down their site.
But let's say they didn't shut it all down in a fit of panic. What could this have accomplished?
It could slow them down.
They're reading emails and passwords off CPanel logs; they're not the NSA. Lots of their work is going to be manual.
If we can load them up with a bunch of fake passwords and emails, we can give the chance for the IT departments to block the domain and issue warnings to students.
We also give ourselves time to reach out to their hosting providers and report abuse.
Is this the correct way to handle the situation?
No. Report it to the authorities and let them deal with it. This is all just hypothetical after all.
This article was heavily helped in creation, content, and misadventure with Evan Conrad. This was cross-posted at dev.to. Hack the Planet!




